You have entered a bunch of RBL’s into your IP Block List Providers. I personally use the four spamhaus providers having great success with these from past experience.

How do you know these RBL’s are working? Where do you get information about what they are doing? Which RBL provider is blocking the most?
Well by default the RBL logs are located under:
C:\Program Files\Microsoft\Exchange Server\TransportRoles\Logs\AgentLog
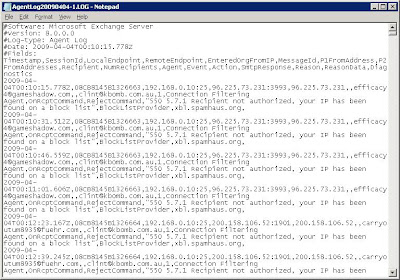
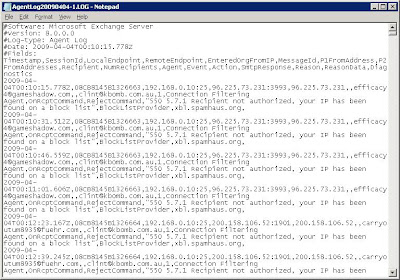
If I crack one of these log files open it will look similar to this:
When an incoming sender’s IP is found in an RBL, the SMTP connection from the sender is dropped and the contents of the spam email will never reach your organisation. Because of this, spam detected by an RBL will never appear in your quarentine mailbox. RBL checks are done before the Exchange Content filter. Most exchange administrators that run RBL's will notice little spam appearing in the spam mailbox because RBL's will filter most the spam out. Additionally mail blocked by an RBL will not appear in the Message Tracking Log which is viewable by typing Get-MessageTrackingLog.
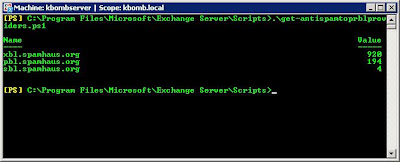
It is possible to get summary information from all the RBL log files by using a powershell script called get-antispamtoprblproviders.ps1 located by default in C:\Program Files\Microsoft\Exchange Server\Scripts

How do you know these RBL’s are working? Where do you get information about what they are doing? Which RBL provider is blocking the most?
Well by default the RBL logs are located under:
C:\Program Files\Microsoft\Exchange Server\TransportRoles\Logs\AgentLog
If I crack one of these log files open it will look similar to this:
When an incoming sender’s IP is found in an RBL, the SMTP connection from the sender is dropped and the contents of the spam email will never reach your organisation. Because of this, spam detected by an RBL will never appear in your quarentine mailbox. RBL checks are done before the Exchange Content filter. Most exchange administrators that run RBL's will notice little spam appearing in the spam mailbox because RBL's will filter most the spam out. Additionally mail blocked by an RBL will not appear in the Message Tracking Log which is viewable by typing Get-MessageTrackingLog.
It is possible to get summary information from all the RBL log files by using a powershell script called get-antispamtoprblproviders.ps1 located by default in C:\Program Files\Microsoft\Exchange Server\Scripts
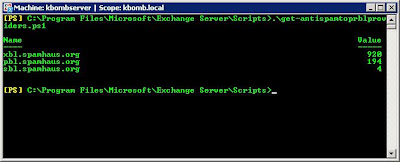
Above the get-antispamtoprblproviders.ps1 script shows a summary of how many emails were blocked by each provider in my exchange organization. This information was produced by searching through my 4 log files.
The get-antispamtoprblproviders.ps1 script also has 3 parameters:
-startdate
-enddate
-top
-startdate
-enddate
-top
Startdate and Enddate explain themselves... however top shows the top providers in order. For example if you wanted to see your top 2 RBL’s blocking the most email you would enter in –top:2
Hope this helps you monitor your RBL providers better.




FYI, the zen.spamhaus.org RBL contains the xbl, sbl, and pbl lists so there's no reason to includes them separately. If you're worried about tracking which list an IP was found on, you can analyze the ZEN return codes found here: http://www.spamhaus.org/zen/
ReplyDeleteReturn Codes
127.0.0.2 SBL
127.0.0.3 CSS
127.0.0.4-8 XBL
127.0.0.10-11 PBL
It helps alleviate some of the load on the Spamhaus servers.