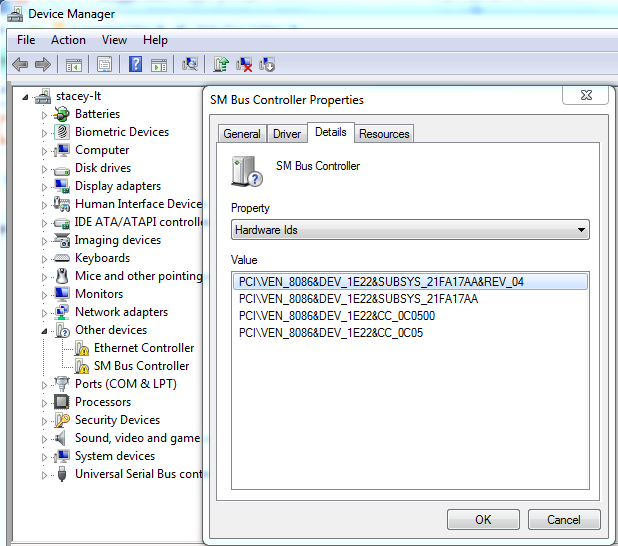
When setting up a new Lenovo X230 for a customer I had problems finding the correct driver for an SM BUS Controller. The hardware had the following Vendor and Device Id's.
PCI\VEN_8086&DEV_1E22&SUBSYS_21FA17AA&REV_04
After research it turns out that this hardware matches a Intel 7 Series/C216 Chipset Family SMBus Host Controller.
To download the Intel 7 Series/C216 Chipset Family SMBus Host Controller driver please see the following website:
http://devid.info/download/56602/27
Scroll through the ads until you find 56602_Chipset_9.3.0.1019.zip (2.87 Mb)
PCI\VEN_8086&DEV_1E22&SUBSYS_21FA17AA&REV_04
After research it turns out that this hardware matches a Intel 7 Series/C216 Chipset Family SMBus Host Controller.
To download the Intel 7 Series/C216 Chipset Family SMBus Host Controller driver please see the following website:
http://devid.info/download/56602/27
Scroll through the ads until you find 56602_Chipset_9.3.0.1019.zip (2.87 Mb)